Descriptio
| ← Previous revision | Revision as of 09:18, 31 October 2025 | ||
| Line 3: | Line 3: | ||
|
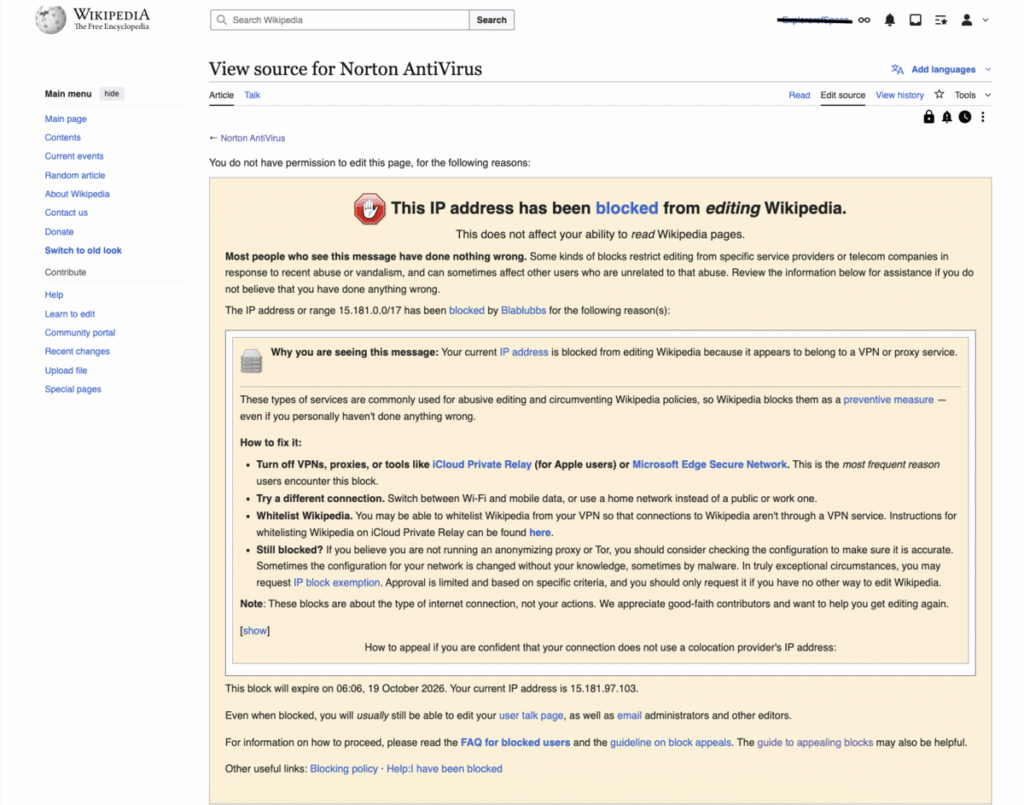
”’VPN blocking”’ is a technique used to block the [[encrypted]] [[protocol tunneling]] communications methods used by [[virtual private network]] (VPN) systems. Often used by large organizations such as national governments or corporations, it can act as a tool for [[computer security]] or [[Internet censorship]] by preventing the use of VPNs to bypass [[network firewall]] systems.
|
”’VPN blocking”’ is a technique used to block the [[encrypted]] [[protocol tunneling]] communications methods used by [[virtual private network]] (VPN) systems. Often used by large organizations such as national governments or corporations, it can act as a tool for [[computer security]] or [[Internet censorship]] by preventing the use of VPNs to bypass [[network firewall]] systems.
|
||
|
==
|
== ==
|
||
|
Blocking VPN access can be done a few different ways. [[Port (computer networking)|Ports]] that are used by common VPN tunneling protocols, such as [[Point-to-Point Tunneling Protocol|PPTP]] or [[Layer 2 Tunneling Protocol|L2TP]], to establish their connections and transfer data can be closed by system administrators to prevent their use on certain networks. Similarly, a service can prohibit access by blocking access from IP addresses and IP address ranges that are known to belong to VPN providers.<ref>{{Cite web|url=https://focsec.com/|title=VPN and Proxy Detection API |website=Focsec|access-date=2025-07-21}}</ref><ref>{{Cite web|url=https://www.ip2location.com/databases/px2-ip-proxytype-country|title=IP2Proxy™ IP-ProxyType-Country Database [PX2]|website=www.ip2location.com|access-date=2016-06-12}}</ref> Some governments have been known to [[IP address blocking|block all access to overseas IP addresses]], since VPN use can involve connecting to remote hosts that do not operate under that government’s jurisdiction.<ref name=globalvoices>{{cite web|last1=Lam|first1=Oiwan|title=China: Cracking down circumvention tools|date=13 May 2011 |url=http://advocacy.globalvoicesonline.org/2011/05/13/china-cracking-down-circumvention-tools/}}</ref>
|
Blocking VPN access can be done a few different ways. [[Port (computer networking)|Ports]] that are used by common VPN tunneling protocols, such as [[Point-to-Point Tunneling Protocol|PPTP]] or [[Layer 2 Tunneling Protocol|L2TP]], to establish their connections and transfer data can be closed by system administrators to prevent their use on certain networks. Similarly, a service can prohibit access by blocking access from IP addresses and IP address ranges that are known to belong to VPN providers.<ref>{{Cite web|url=https://focsec.com/|title=VPN and Proxy Detection API |website=Focsec|access-date=2025-07-21}}</ref><ref>{{Cite web|url=https://www.ip2location.com/databases/px2-ip-proxytype-country|title=IP2Proxy™ IP-ProxyType-Country Database [PX2]|website=www.ip2location.com|access-date=2016-06-12}}</ref> Some governments have been known to [[IP address blocking|block all access to overseas IP addresses]], since VPN use can involve connecting to remote hosts that do not operate under that government’s jurisdiction.<ref name=globalvoices>{{cite web|last1=Lam|first1=Oiwan|title=China: Cracking down circumvention tools|date=13 May 2011 |url=http://advocacy.globalvoicesonline.org/2011/05/13/china-cracking-down-circumvention-tools/}}</ref>
|
||